 Operational Security (OPSEC). Wikipedia describes OPSEC as the process of protecting individual pieces of data that could be grouped together to give the bigger picture (called aggregation).
Operational Security (OPSEC). Wikipedia describes OPSEC as the process of protecting individual pieces of data that could be grouped together to give the bigger picture (called aggregation).
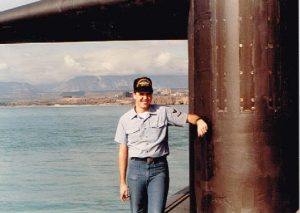
Loose lips sink ships! One of the best slogans of WWII. I am a former US Navy Cryptologist who deployed on US Navy Submarines. In fact, I earned the coveted Dolphins (Qualified in Submarines); part of OPSEC every submariner is taught dates to 1943.
Congressman Andrew J. May was Chairman of the Committee of Military Affairs during WWII. In the Spring of 1943, Congressman May toured the Pacific bases and received briefings on why the Japanese Anti-Submarine Warfare (ASW) depth charge efforts were unsuccessful. The Japanese did not know our submarines could reach depths deeper than their submarines, and were setting the depth charges several hundred feet short.
Congressman May held a press conference in June 1943 and made the statement “Don’t worry about our submariners, the Japanese are setting their depth charges too shallow.” The press reported that statement and within 24 hours the Japanese were setting their depth charges to a deeper setting. After the end of the war Admiral Charles Lockwood, Commander Submarine Forces Pacific (COMSUBPAC) wrote “I consider that indiscretion cost us ten submarines and 800 officers and men.”
Good history lesson, but how does this apply to me?
The LTPAC Clinician is the definition of a mobile medical professional. Every conversation, computer interaction, discussion with colleagues, etc. are done in a place where others can listen or intercept communications that are intended to be private.
For example, how many clinicians have taken a call from a facility about a patient and had the discussion, including status and treatment decisions, in line while waiting for coffee? Discussed a specific case with colleagues at lunch in a restaurant? Used an open Wi-Fi connection? Received a call from a child of a patient and discussed patient specifics without validating the HPAA Privacy Notice? Use a mobile device without encryption on it?
OPSEC is a five-step iterative process that assists an organization in identifying specific pieces of information requiring protection and employing measures to protect them.
-
- 1.Identification of Critical information. Classification of information is always the first step. You must know what protection levels are required for each classification. PHI needs more protection than your office phone bill.
-
- 2. Analysis of Threats. Threats are not just people trying to steal information. What if the lunch you had with your colleague in the restaurant happens to be next to the family of the patient?
-
- 3. Analysis of Vulnerabilities. Vulnerabilities are what a threat would use to attack you and can be Technical, Physical or Administrative in nature. OPSEC is focusing on the USE of these three areas.
-
- 4. Assessment of Risk. Ongoing process of identification, mitigation steps, and execution.
-
- 5. Application of Appropriate OPSEC Countermeasures. Mitigation steps are Countermeasures. They counter the risk (no open Wi-Fi use without VPN for example) and exposure.
OPSEC must be included as part of the overall Risk Assessment process every LTPAC Medical Group is required to do by HIPAA. Risk Assessment is not just about the Technical safeguards on your system(s). It also includes Physical and Administrative safeguards. For your practice, you may determine that a policy to not use open W-Fi devices is needed or a policy on how information is disclosed to family members after checking the HIPAA Privacy Notice.
Each individual practice will have risks and mitigation steps that need to be identified and ultimately executed. And every year new operational risks will be identified as technology and process changes. An example: How will your practice use Telemedicine and how will you address operational risks?
People are trying to do their jobs. You need to give them the tools and awareness to do that job in a safer manner for your organization.
